The Contrast API can be utilized to quickly identify applications using vulnerable log4j libraries.
API
{{CONTRAST_URL}}/{{CONTRAST_API_URL}}/{{CONTRAST_ORG_UID}}/libraries/filter?expand=apps,skip_links&q=log4j-core&quickFilter=ALL
Example of the API request via CURL
curl --location --request GET 'https://app.contrastsecurity.com/Contrast/api/ng/37472d1b-d5b7-474c-9011-314a144464c2/libraries/filter?expand=apps,skip_links&q=log4j-core&quickFilter=ALL' \
--header 'Authorization: <auth>' \
--header 'API-Key: <key>'
- To fill in the auth, In the Contrast UI go to your User Settings in the top right corners drop down menu.
- Under Profile there will be a section called YOUR KEYS
- Click on Copy under Authorization Header and put that in place of <auth>
- Select the API Key hash, copy and replace <key>
Result should look something like this.
curl --location --request GET 'https://app.contrastsecurity.com/Contrast/api/ng/37472d1b-d5b7-474c-9011-314a144464c2/libraries/filter?expand=apps,skip_links&q=log4j-core&quickFilter=ALL' \
--header 'Authorization: emVuY2lkQGdtYUlsLmNveTpOS1BHNTVaSFY4OTc3STc5' \
--header 'API-Key: H6j8Z1vFjz58SShUq3bg5EW61Md19E5I'
This can be run from a command line or copied into postman to get the JSON results.
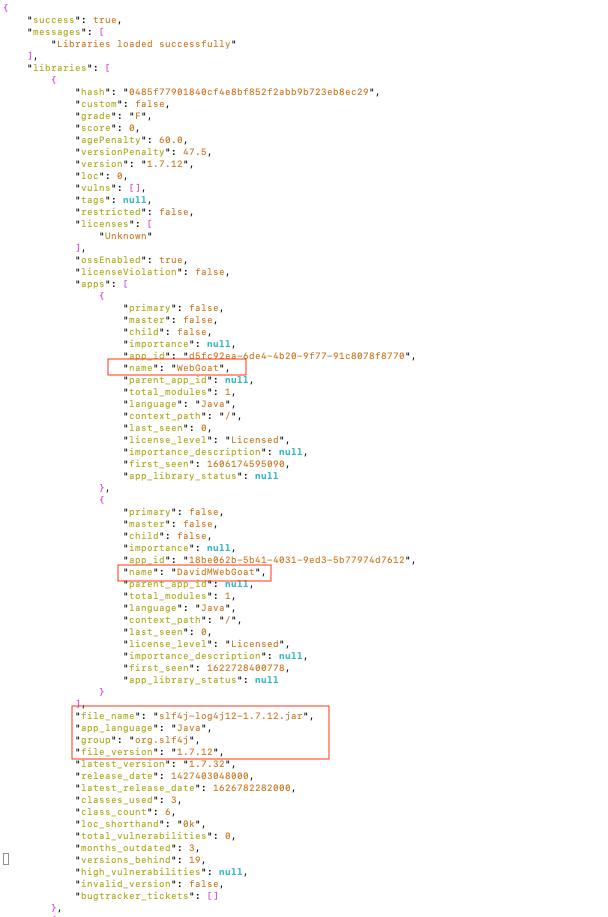
Example of what to look for in the JSON