Overview
The Contrast-Slack integration can push vulnerability, attack, and server-related updates directly to Slack channels to keep organizations aware of the latest security posture of their applications. Users who benefit from this integration include developers, security engineers, security managers, and operations analysts.
Our integration with Slack is similar to the Microsoft Teams integration.
Table of Contents
Before you start
-
All Contrast Security integrations require an Organization Administrator in order to set up the connection
Set up the integration
-
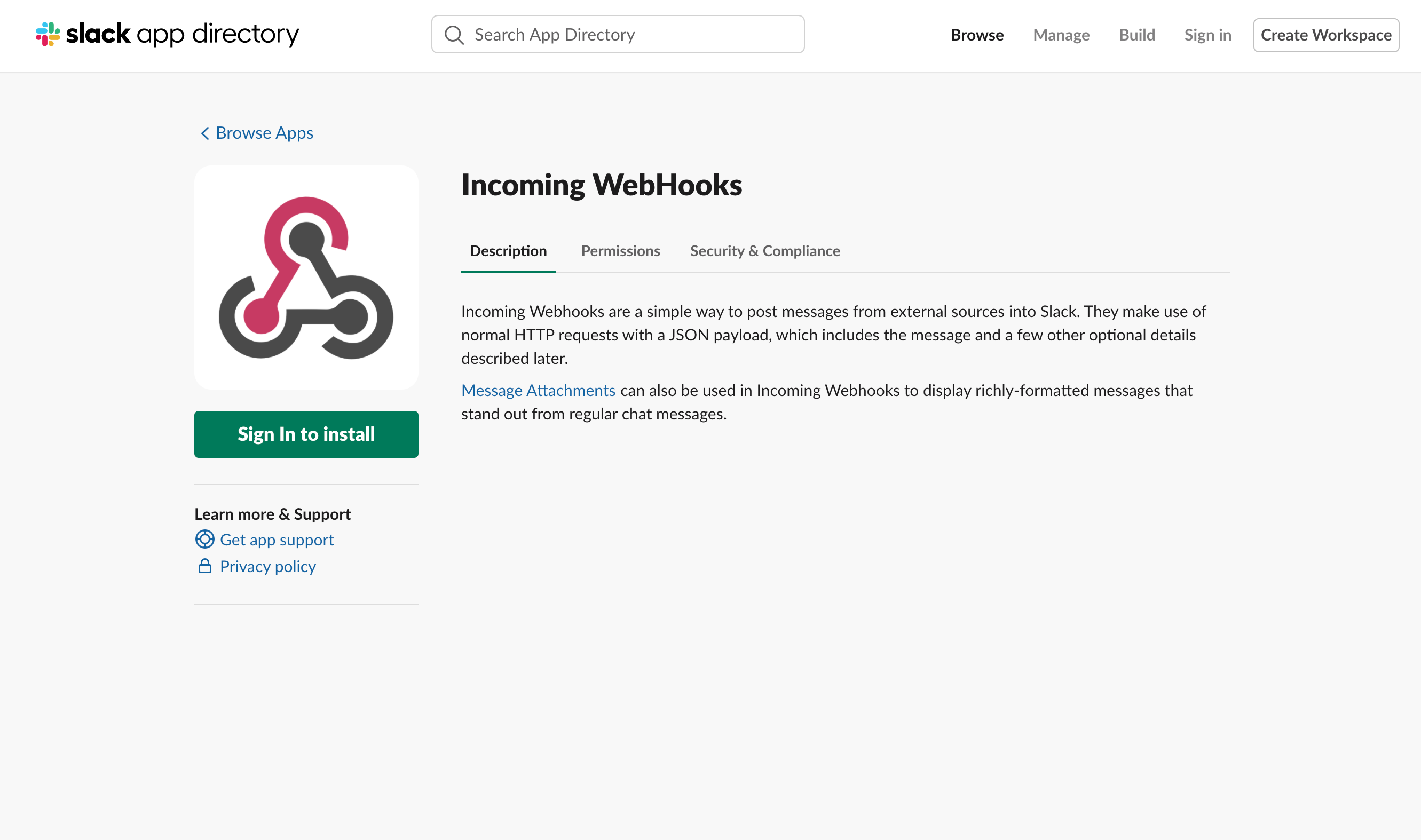
Install the Slack app “Incoming webhooks” onto your Slack organization.
2. Choose a Slack channel where you would like Contrast to post security messages.
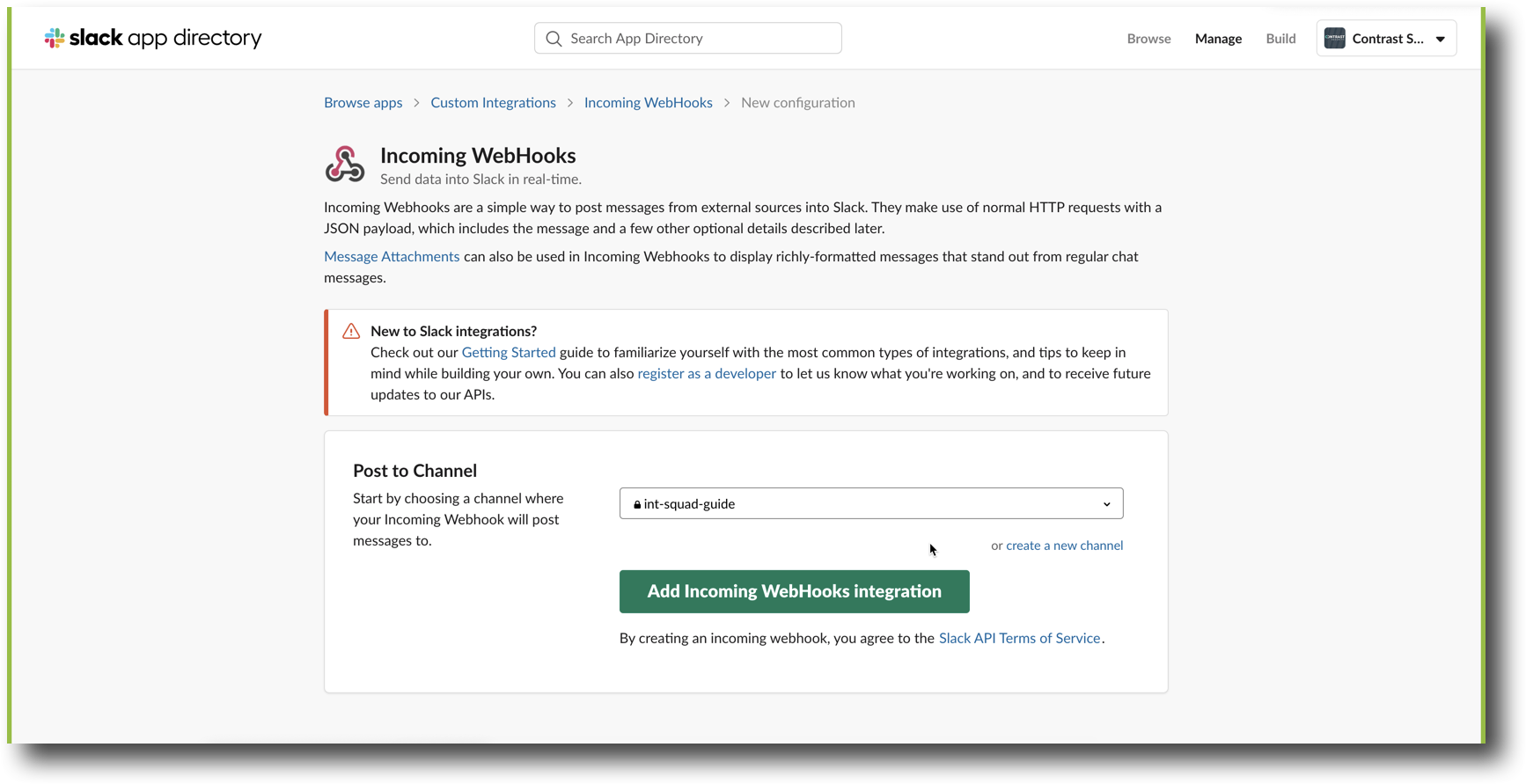
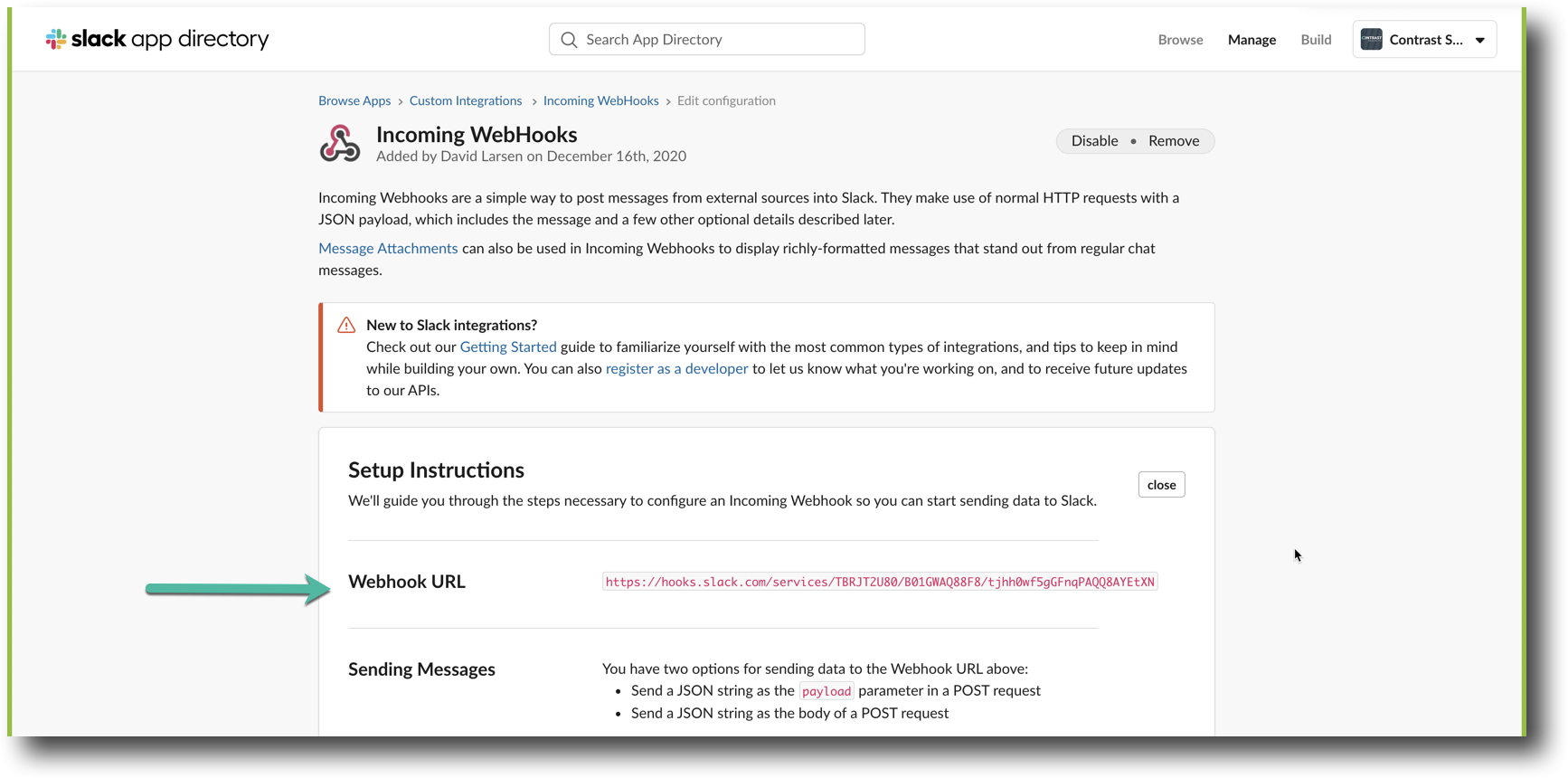
3. Once you select a channel and click “Add Incoming WebHooks Integration” button from the picture above, you’ll receive a WebHook URL. Copy the URL.
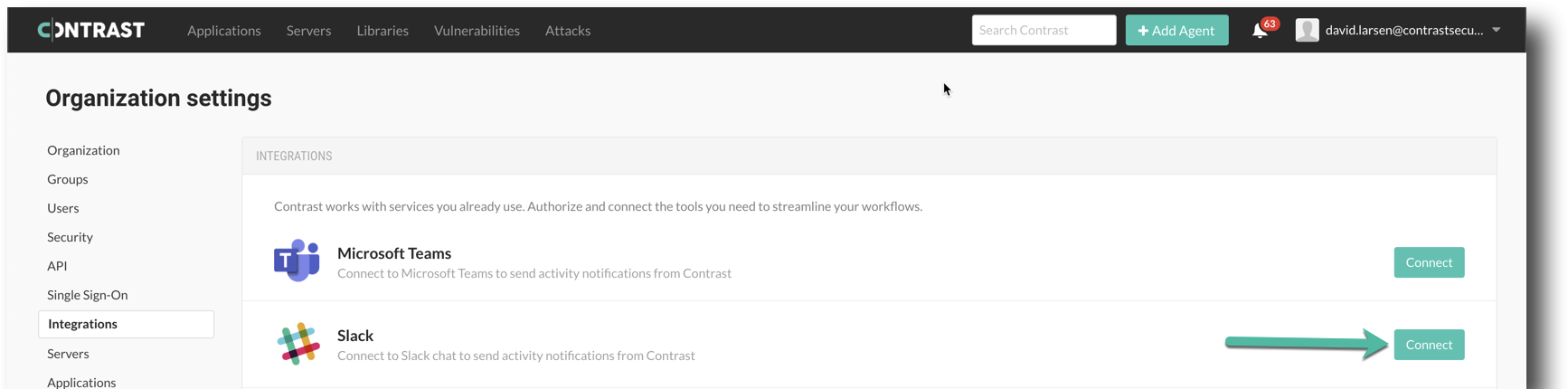
4. In Contrast UI, from the Organization settings dropdown menu item, navigate to the Integrations page. Click on Connect in the Slack row item.
5. Define a Name for your configuration. Paste the Webhook URL you obtained from Step 3. Also, choose the set of Applications to which this configuration should apply.
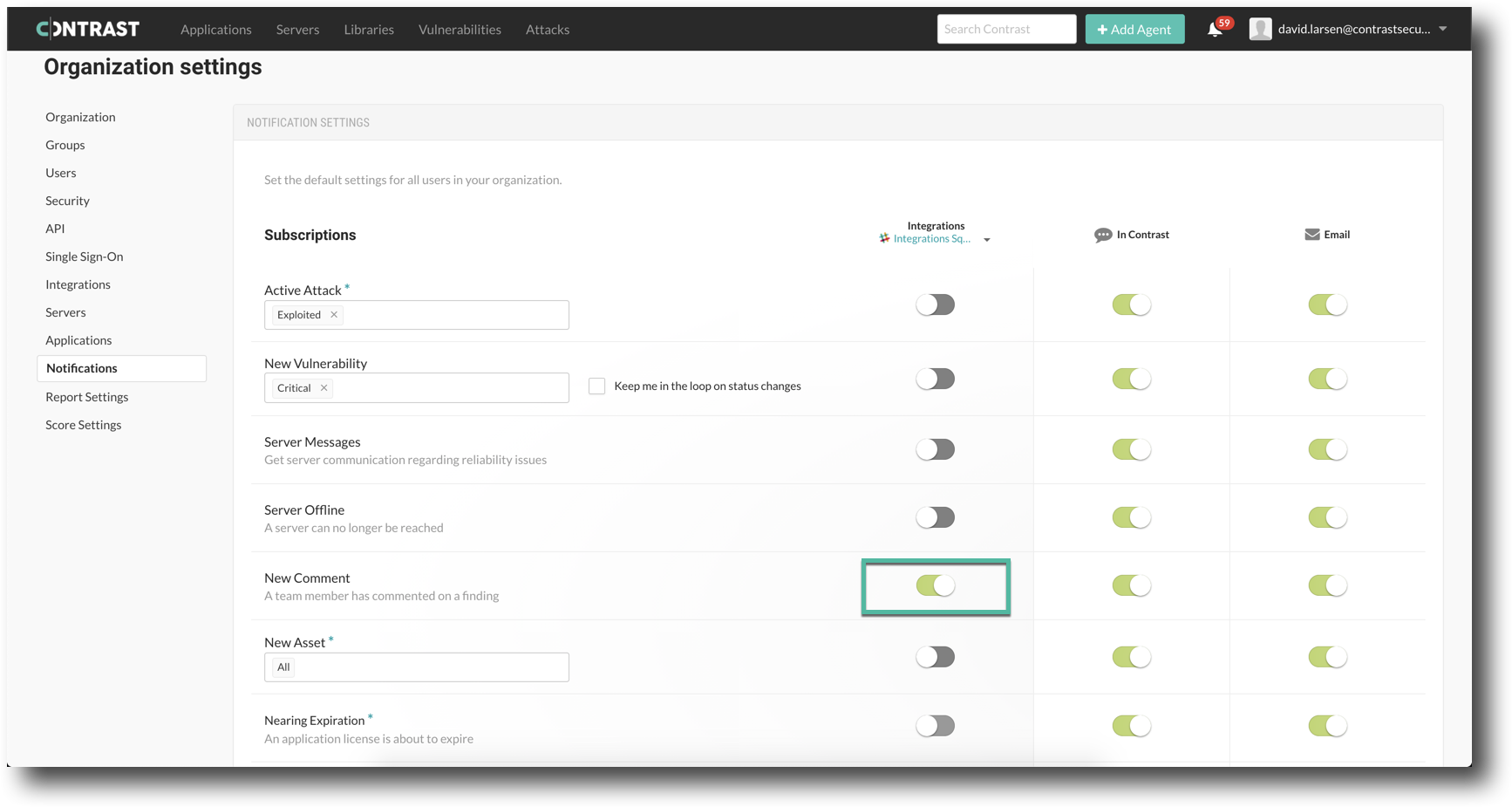
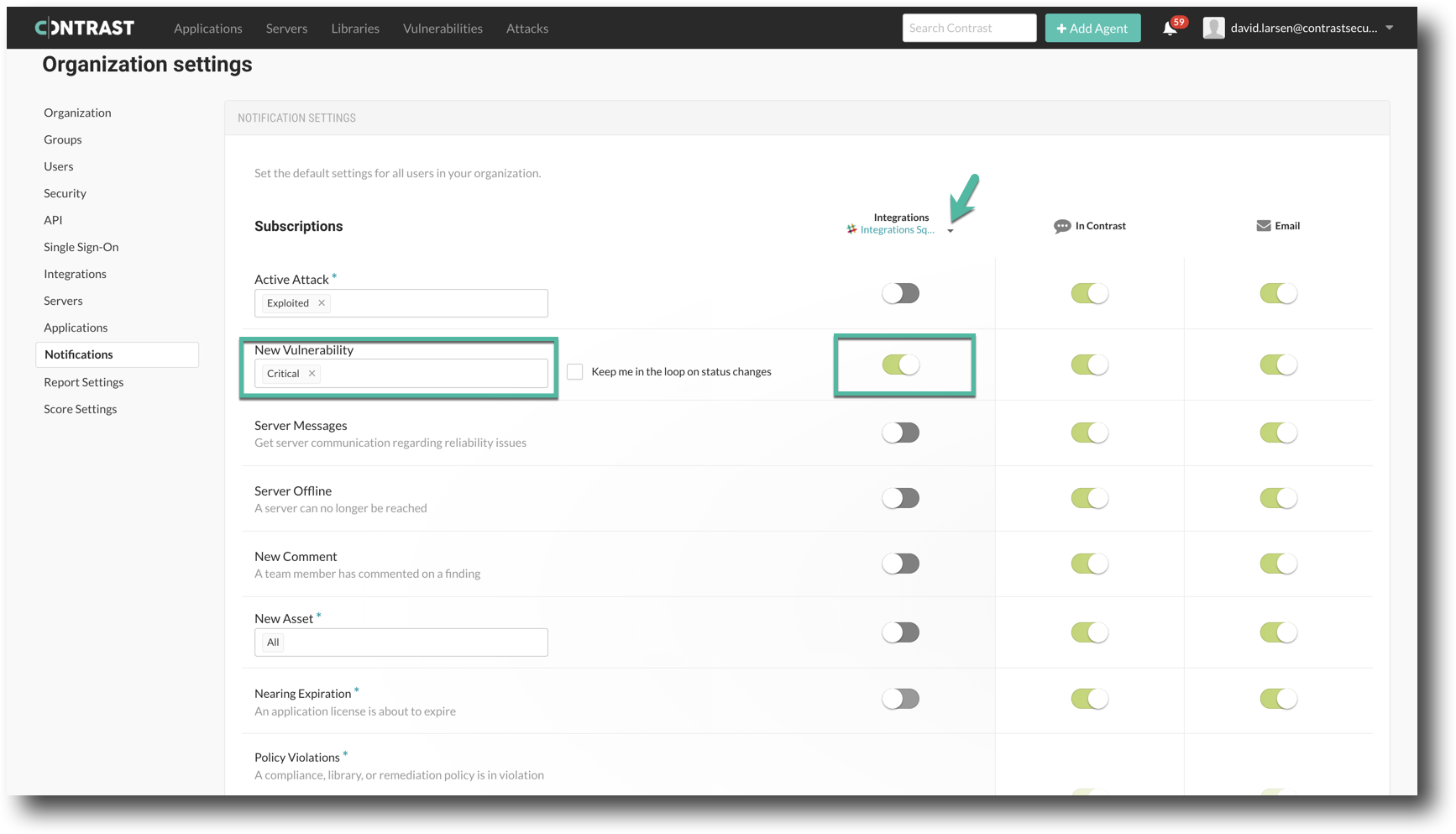
You can choose which events to be notified about from the Notifications page on the left hand side of the page (:green_star:). The section below on use cases recommends which events to subscribe to for certain notifications.
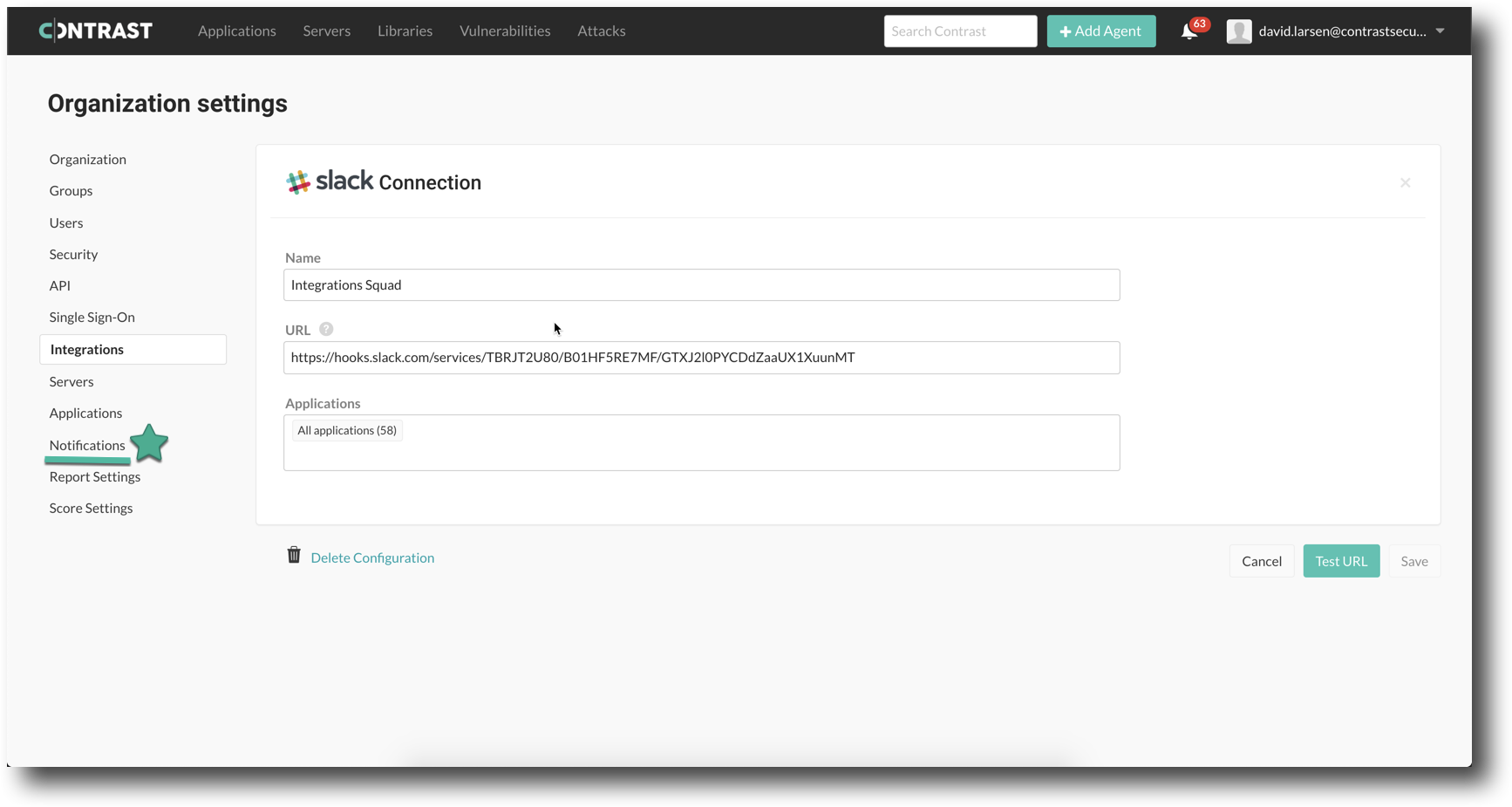
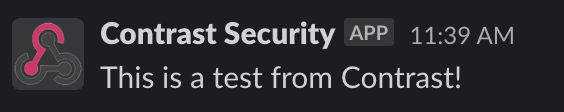
6. At the bottom right, click the Test URL button to ensure that the URL is valid. Once you see a message in the slack room you’ve chosen saying that the test is successful, click Save.
For an unsuccessful test, check that the URL you received from Slack and the one you posted in Contrast are matching. Contact Contrast Support (support@contrastsecurity.com) if necessary.
Meet your use case
a. Alert developers about critical vulnerabilities
Developer’s needs to know when critical vulnerabilities are found in an application they develop, so they can more quickly respond to them by kicking off the triage process earlier.
To receive notifications about new critical vulnerabilities in Slack, he’ll need to toggle the switch in the row item named “New Vulnerability” illustrated by the below screenshot.
Developers would also like to know when his team adds comments to vulnerabilities Contrast has discovered, so that they can stay in the loop and contribute to the conversation around remediation.
b. Let application security teams know when a new application is onboarded
Security Managers would like to make sure that Contrast is running on all the organization’s applications and QA servers. They have sent instructions to the operations team and would like to monitor the progress of Contrast roll out as systems come online.
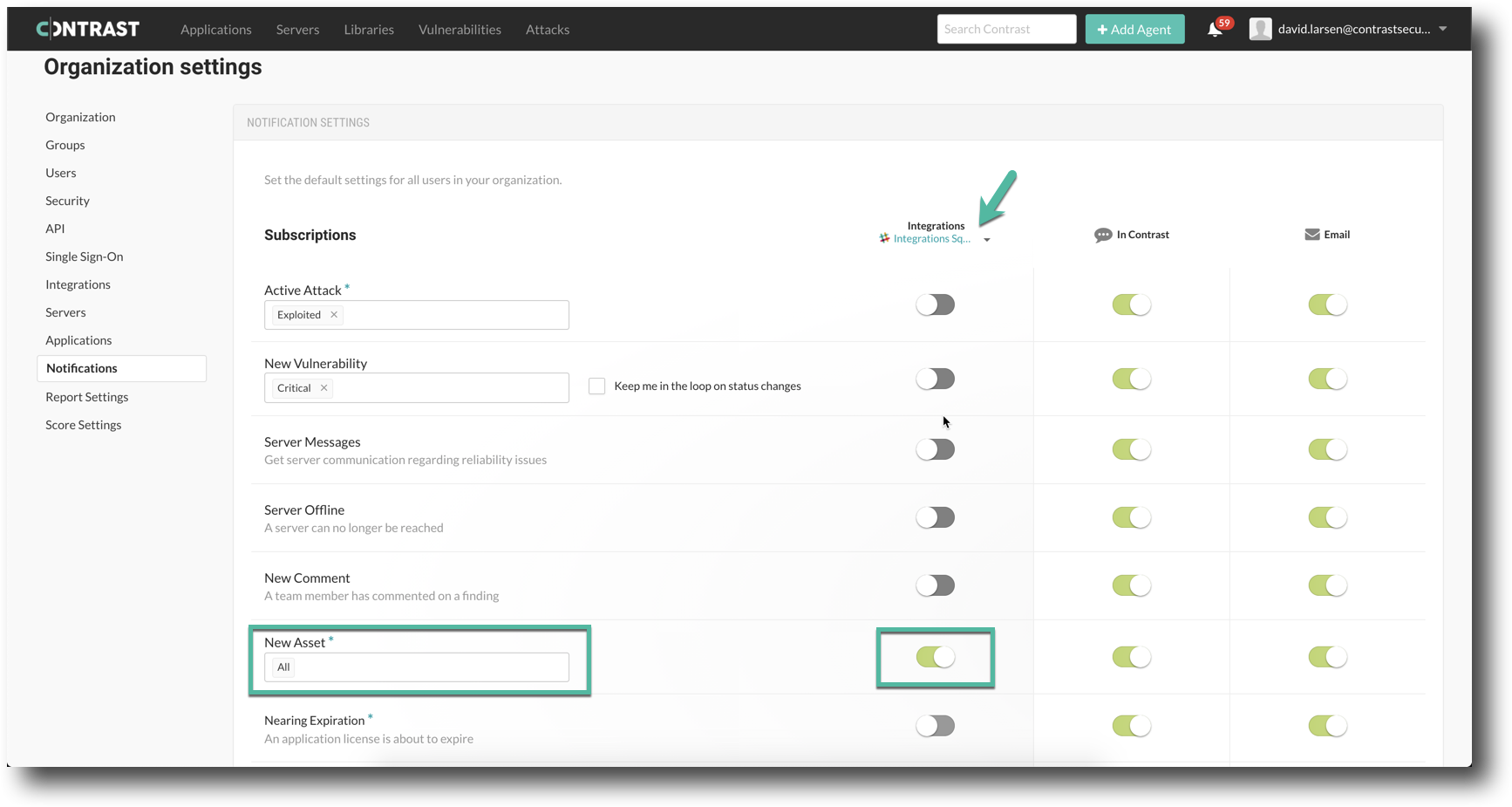
To be notified in a Slack channel when new applications or servers (i.e. assets) come online, they’ll need to toggle the switch in the row item named “New Asset” illustrated by the below screenshot.
c. Inform operations analysts when applications are being attacked
People in the network operations center wants to be alerted when a new attack comes in, so they can immediately investigate and take defensive action if necessary.
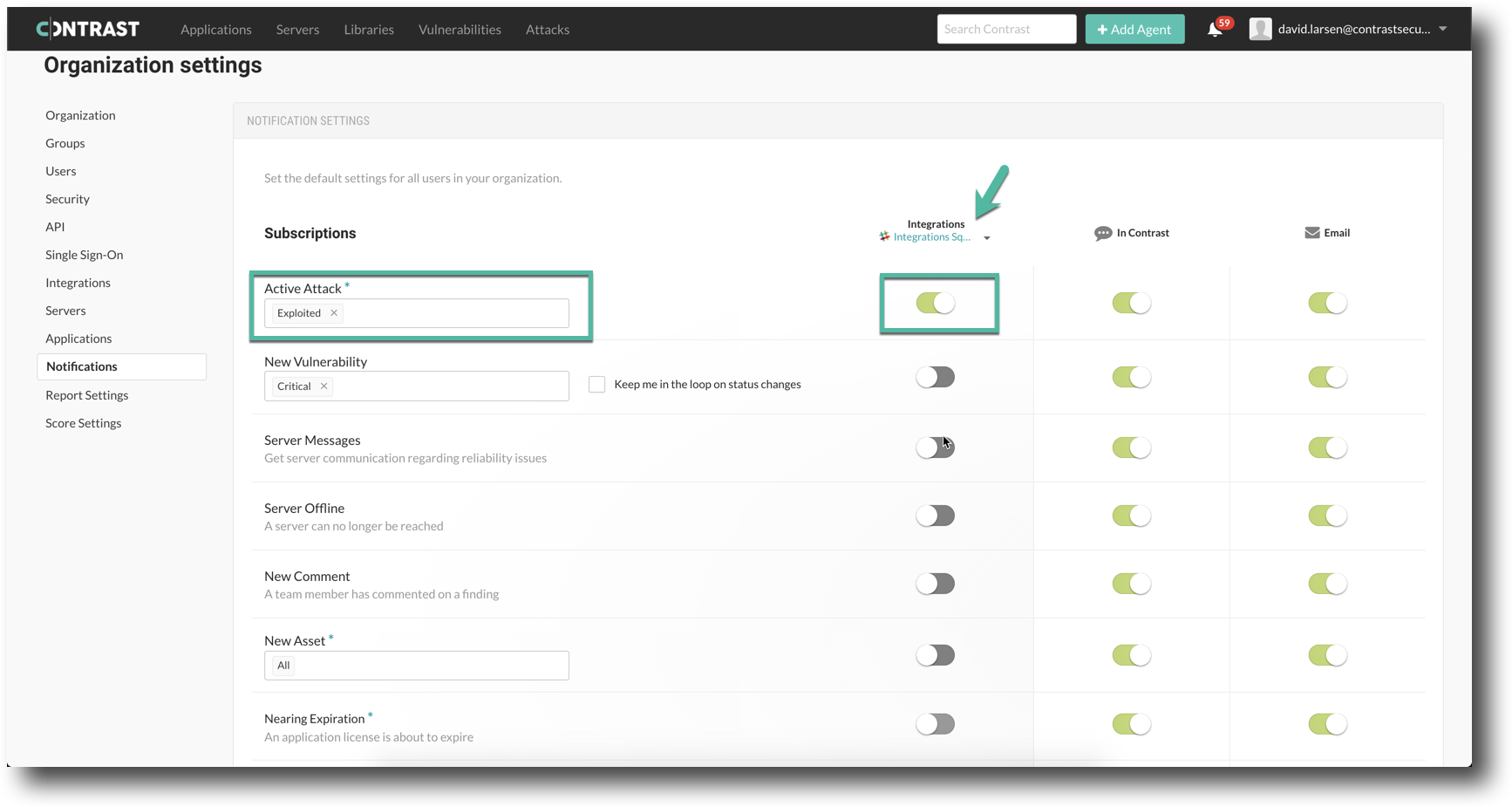
To receive notifications for attack events, toggle the switch in the row item named “Active Attack” illustrated by the below screenshot. They can subscribe to any of the following active attacks: Probed, Probed (P), Blocked, Blocked (P), Suspicious, and Exploited. The (P) qualification indicates that the action (i.e. Block or Probe) occurred at the (P)erimeter of the application.
d. See new comments/ assist/ decrease triage time
Developers like to work fast. They believes in collaborating asynchronously. To this point, they would like to make use of Slack for triaging open vulnerabilities with his team. In order to speed up this triage time they would like to have all new comments made on Contrast Vulnerabilities show up in Slack.
To be able to see new comments on vulnerabilities show up in the Slack channel you’ll want to configure the notification setting as the below screenshot indicates